A good password policy is the first step on securing your environment and company data. Without a password policy in place you can be sure that a lot of users will take a password that can be easily guessed/brute forced in less than 5 minutes. The table below will show the 5 most used passwords of 2019. As you can see, they are not safe.
| 1 | 12345 |
| 2 | 123456 |
| 3 | 123456789 |
| 4 | test1 |
| 5 | password |
Have a look at the Microsoft Password Guidance for more information about passwords.
Azure AD Only
Default password policy
When using Azure Active Directory on its own (no on-premises AD with Azure AD Connect) you automatically make use of the Azure AD password policy. Look at the requirements below or take a look at the Microsoft documentation.
| Property | Requirements |
| Characters allowed | A – Z a – z 0 – 9 @ # $ % ^ & * – _ ! + = [ ] { } | \ : ‘ , . ? / ` ~ ” ( ) ; blank space |
| Characters not allowed | Unicode characters. |
| Length constraints | A minimum of 8 characters and a maximum of 256 characters. |
| Password restrictions | Requires three out of four of the following Lowercase characters. Uppercase characters. Numbers (0-9). Symbols (see the previous password restrictions). |
| Password expiry | Default value is 90 days. |
| Password expiry notification | Default value is 14 days. |
| Password change history | The last password can’t be used again when the user changes a password. |
| Password reset history | The last password can be used again when the user resets a forgotten password. |
| Account lockout | After 10 unsuccessful sign-in attempts with the wrong password, the user is locked out for one minute. Further incorrect sign-in attempts lock out the user for increasing durations of time. Smart lockout tracks the last three bad password hashes to avoid incrementing the lockout counter for the same password. If someone enters the same bad password multiple times, this behavior will not cause the account to lock out. |
On top of the requirements above all Azure AD tenants use Azure AD Password Protection. This feature will eliminate all weak password by blocking known weak passwords.
Global banned password list
Microsoft has a list of global banned passwords that is kept up-to-date by analyzing Azure AD security telemetry data. They look for commonly used passwords that are weak and/or compromised. It’s important to note that Microsoft doesn’t use third-party/public password lists – all data is coming from Azure AD itself.
Custom banned password list
It’s possible to add a custom banned password list on top of the global list. This way you can block passwords that are primarily focused on organizational-specific terms like brand names and product names.
Password evaluation
Microsoft uses the lists above to determine if a passwords is considered safe. To assess the strength of a new password, Microsoft will go through a few steps and will accepted or reject based on the outcome. You can some neat documentation on this but i’ll add a brief overview for completeness.
- Normalization is used to map a small set of passwords to a much larger set. They’ll replace all uppercase letters with smallercase and common character substitutions are performed (an ‘O’ becomes an ‘0’, an ‘I’ becomes a ‘1’, …)
- Fuzzy matching is applied on the normalized passwords, based on an edit distance of one comparison. If ‘AzureScene’ is on the password list and a users changes his password to ‘BzureScene’ the password is denied because it is within an edit distance of 1 of AzureScene.
- Substring matching is applied on the normalized passwords. Substring matching will look for the first name, last name en tenant name in the password.
After applying all steps above a password score will be calculated. A score of at least 5 is required for the password to be accepted.
- Each banned word is given 1 point.
- All remaining characters are given 1 point each.
How to improve?
Disable password expiration
Microsoft recommends disabling password expiration. Note that you should definitely configure multi-factor authentication before doing this!
- Navigate to the Microsoft 365 Admin Center and log on with a global administrator.
- Click on Settings followed by Security & Privacy.
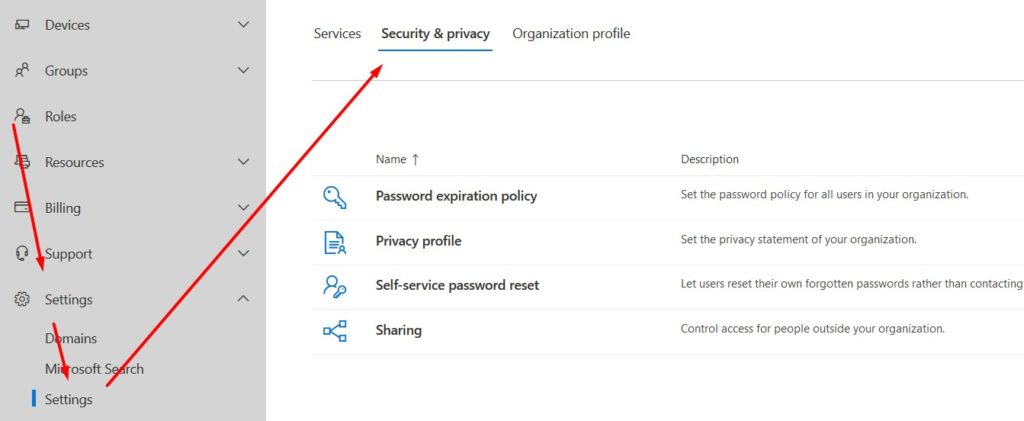
- Select Password expiration policy and deselect Set user passwords to expire after a number of days.
Configure custom smart lockout settings
Smart lockout can block attackers who are trying to guess you users’ passwords. Smart lockout can recognize sign-ins coming from valid users and therefore can lock out the attacker while letting your users continue to access their accounts. Smart lockout is included in all Azure AD tenants but custom settings will require Azure AD P1 or P2.
- Navigate to the Azure portal and log on with an account that has appropriate permissions.
- Open the Azure Active Directory blade and click Security. You’ll find this within the ‘Manage’ area.
- Select Authentication methods.
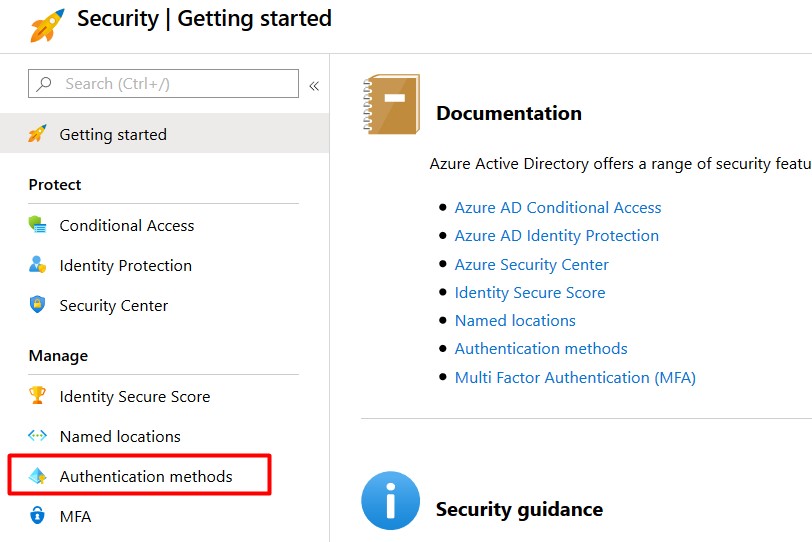
- Select Password protection.
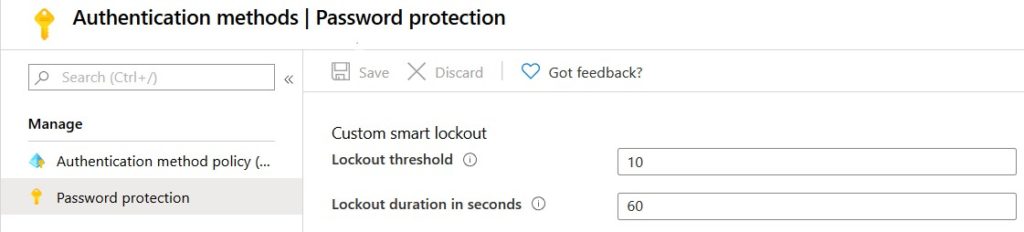
- Configure the lockoust threshold and lockout duration in seconds as desired. The default settings are pretty good to start (You don’t need to do anything to enable this).
Configure custom banned passwords
Customer banned passwords are configured in the same blade as custom smart lockout (look above).
- Navigate to the Azure portal and log on with an account that has appropriate permissions.
- Open the Azure Active Directory blade and click Security. You’ll find this within the ‘Manage’ area.
- Select Authentication methods.
- Select Password protection.
- Enable Enforce custom list.
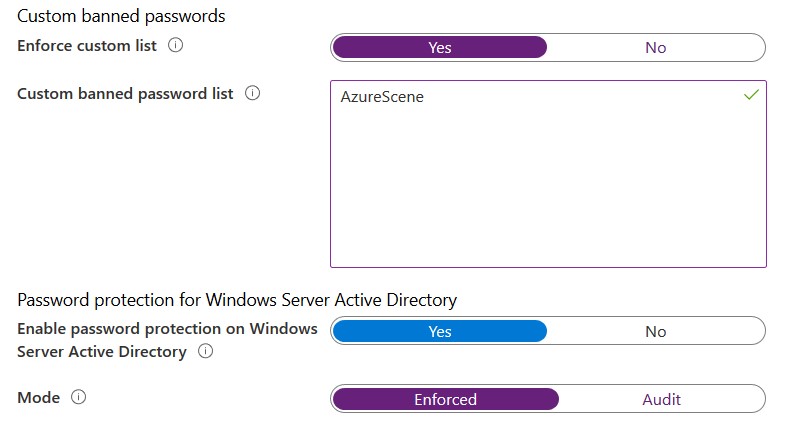
- Add words to your custome list.
- Optionally: Enable password protection on Active Directory. An agent on your domain controller is required for this to work (look below).
- Set the mode to Enforced.
Monitor users at risk
Configure Azure AD Identity Protection including email notifications to monitor leaked credentials, risky sign-ins and more. Look at my blog post on Azure AD Identity Protection for more information.
Enable self-service password reset
Self-service password reset gives your users the ability to reset their password or unblock their account without a call to support.
Go passwordless
Microsoft recommends going passwordless. This feature is beyond the scope of this blog posts but will be added in the near future.
Active Directory & Azure AD Connect
When using an on-premises Active Directory the default Azure AD password policy isn’t used. Without a local password policy, users can change their passwords to whatever they like and it will get synchronized to Azure AD. That’s why you must configure an on-premises password policy.
Configure on-premises password policy
By default, every Active Directory has a password policy in place. It’s a computer (not user!) setting in the Default Domain Policy. This policy will configure the active directory on all domain controllers to enforce the configured settings. By default, only one password policy is possible per domain and all users will have the same password policy. However, it’s possible to extend this by using a fine-grained password policy.
To edit the default password policy, you need to edit the Default Domain Policy. You can find all password settings under Computer Configuration > Policies > Windows Settings > Security Settings > Account Policies > Password Policy.
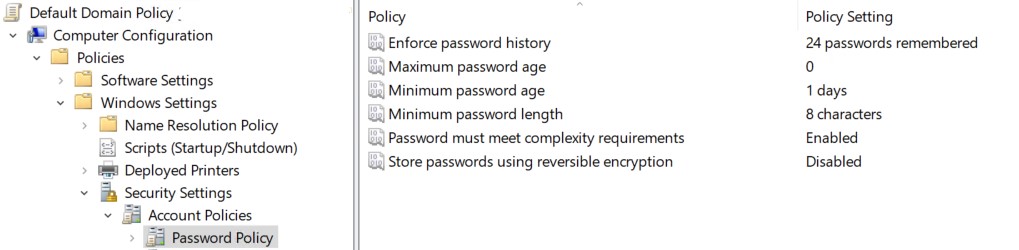
Enforce password history
This policy will set how many times a password can be reused. There is no best practice but a minimum of 5 looks decent. When you set passwords to not expire (as you should) 5 is perfect.
Maximum & minimum password age
Minimum password age will set the minimum amount of days a user needs to keep his new password before it can be changed again. The maximum password age will set the days after which a password will expire.
Disabling password expiration is the new standard. That’s why Maximum password age should be set to ‘0’. The minimum password age should be set to 1 or more in order for for the password history setting to work.
Minimum password length
The minimum password length. A minimum of 8 character will align this to the Azure AD password policy. A password length under 7 is considered unsafe.
Passwords must meet complexity requirements
This setting should be enabled. Passwords must meet the complexity described below.
- Not contain the user’s account name or parts of the user’s full name that exceed two consecutive characters
- Contain charaters from three of the following categories.
- Uppercase characters (A – Z
- Lowercase characters (a – z)
- Base digits (0 – 9)
- Non-alphabetic charactesr (!$#%…)
Store passwords using reversible encryption
This should be disabled. When enabled, it’s possible to decrypt all the encrypted passwords in AD.
Enable Azure AD Password Protection
It’s possible to enable Azure AD Password protection for on-premises domain controllers. If configured, changing or resetting a password on-premises will use the same global and custom banned list as a password change in Azure AD.
Azure AD Password Protection requires an agent to be installed on every domain controller. Password change/reset requests that are sent to a domain controller without the agent won’t use password protection.
Installing the Azure AD Password Protection agent is currently beyond the scope of this post.
What about account lockout?
Enabling the account lockout policy seems like a nice idea at first but should not be taken lightly. An attacker that has access to a computer in your domain can easily block everyone in minutes.
An attacker can check the active password policy with a simple command (net accounts /domain). No administrator permissions are required. If a lockout threshold is in place the attacker can continue on getting all users in the directory with another command that doesn’t need administrator permissions (wmic UserAccount Get Name).
After getting al the users you can easily run a loop that will try to log on with every user of the list and a random password. As soon as you hit the lockout threshold you’re on to the next one. The entire domain can be locked out in a matter of minutes.
In large environments I advise you to not configure an account lockout policy.
That’s it, you’re all set and a bit more secure!
It is incorrect to say that only one password policy is possible per domain. Fine-Grained Password Policy allows you to have multiple password policies in a domain. This has been around since Server 2008, so it’s not something new.
That’s correct!
[…] La política de contraseñas de Azure AD | escena azul […]
[…] The Azure AD Password Policy – Azure Scene […]
It looks like there is no way to set a minimum password age if your accounts are only in the cloud. Is that correct?
That’s correct!
[…] The Azure AD Password Policy – Azure Scene […]
The on-prem AD password policy will apply only to the synced Azure AD users, right?
Users that are created in Azure AD still use the cloud password policy, and not the policies in on-prem AD. Am I correct here?
Yes, only the synced users.
Thank you for writing this up Jente. I have two quick questions:
1. Is there anyway to prevent passwords from being reused if a native Azure (not synced to on-prem AD) simply resets their password instead of changing their password?
2. What is the difference between Audit mode and Enforced mode for Azure password protection?
Thank you!